Digital Evidence Management – DEM

In today’s digital age, the volume and complexity of digital evidence in investigations have increased exponentially. From law enforcement agencies to corporate investigations, the management of digital evidence has become a critical challenge. This is where Digital Evidence Management (DEM) steps in, revolutionizing the way evidence is collected, organized, analyzed, and presented.
DEM encompasses a range of technologies and processes designed to handle digital evidence efficiently and securely throughout its lifecycle. It not only ensures the integrity and authenticity of digital evidence but also enhances collaboration, accessibility, and effectiveness in investigations. As digital footprints become more pervasive, DEM becomes an indispensable tool in the pursuit of justice and truth.
In this article, we will explore the concept of Digital Evidence Management, its benefits, challenges, and its transformative impact on investigations. We will delve into the innovative approaches and technologies that empower investigators to navigate the complex world of digital evidence with greater efficiency, accuracy, and confidence.
The Growing Challenge of Digital Evidence
In today’s digital landscape, the exponential growth of digital evidence has become a significant challenge for investigations. The sheer volume and complexity of digital data, including emails, social media content, surveillance footage, and more, have made it increasingly difficult to effectively manage, analyze, and present evidence.
Digital evidence poses unique challenges compared to traditional forms of evidence. It can be easily altered, deleted, or concealed, requiring investigators to employ advanced techniques to ensure its integrity and authenticity. Additionally, the dynamic nature of technology demands continuous adaptation of investigative tools and skills to keep pace with emerging digital threats.
The storage, organization, and accessibility of digital evidence further complicate the investigative process. Traditional paper-based systems struggle to handle the diverse formats and massive quantities of digital evidence, calling for specialized solutions and methodologies.
Recognizing the importance of managing digital evidence, Digital Evidence Management (DEM) has emerged as a crucial discipline. DEM encompasses technologies, protocols, and best practices that facilitate the efficient and secure handling of digital evidence throughout the investigative lifecycle.
As the reliance on digital evidence continues to grow, the effective management of this evidence is paramount. Embracing robust DEM strategies is essential for law enforcement agencies, legal professionals, and organizations to navigate the challenges posed by digital evidence and ensure accurate and reliable outcomes in investigations.
Understanding Digital Evidence Management (DEM)
Digital Evidence Management (DEM) refers to the comprehensive approach and set of processes and technologies designed to handle digital evidence effectively and efficiently throughout its lifecycle. DEM encompasses various stages, including the acquisition, storage, analysis, and presentation of digital evidence.
It aims to ensure the integrity, authenticity, and accessibility of digital evidence while minimizing the risk of tampering or mishandling. By employing specialized software, encryption techniques, metadata analysis, and secure storage systems, DEM enables investigators to streamline the management of digital evidence, enhance collaboration among stakeholders, and facilitate the successful resolution of cases.
DEM is a critical component in modern investigations, empowering investigators to navigate the complexities of digital evidence in a structured and reliable manner.
The Benefits of DEM in Investigations
Digital Evidence Management (DEM) brings significant advantages to the realm of investigations. Firstly, DEM streamlines the entire process of managing digital evidence, making it easier to organize, search, and retrieve relevant information efficiently. This leads to time savings and improved productivity for investigators.
Secondly, DEM enhances collaboration among investigative teams by providing secure and centralized platforms for sharing and analyzing digital evidence. This facilitates seamless information sharing, real-time collaboration, and a more coordinated approach to investigations.
Thirdly, DEM ensures the integrity and authenticity of digital evidence through strict chain of custody protocols, encryption techniques, and tamper-proof storage solutions. This ensures that evidence is admissible in court and maintains its evidentiary value.
Furthermore, DEM incorporates advanced analytics capabilities, enabling investigators to extract valuable insights from large volumes of digital evidence. This helps uncover patterns, connections, and crucial information that may have otherwise gone unnoticed, ultimately strengthening investigations.
Overall, DEM optimizes the management and utilization of digital evidence, leading to improved efficiency, enhanced collaboration, greater evidentiary integrity, and more effective investigations.
Key Components of DEM
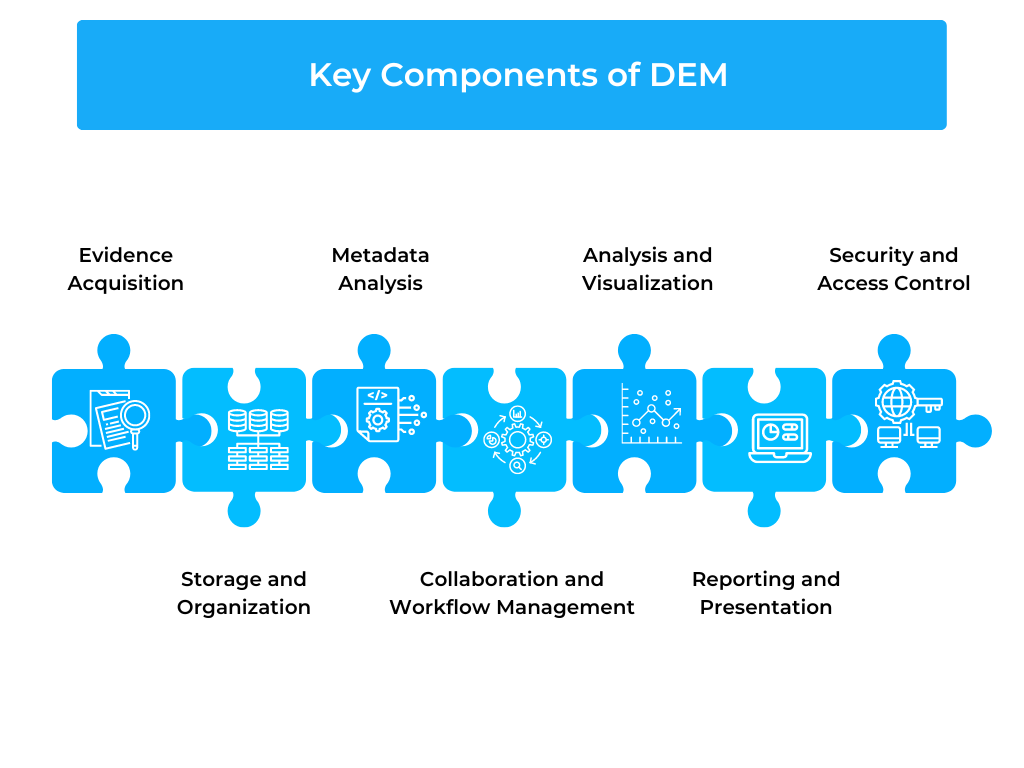
Digital Evidence Management (DEM) comprises several essential components that work together to facilitate the effective handling of digital evidence throughout the investigative process. These components include:
Evidence Acquisition: The process of collecting digital evidence from various sources, such as computers, mobile devices, cloud services, and surveillance systems. It involves techniques like forensic imaging, data extraction, and preservation of evidence in a forensically sound manner.
Storage and Organization: The secure storage and organization of digital evidence to ensure its integrity, accessibility, and chain of custody. This includes the use of robust storage systems, metadata management, and structured categorization of evidence for easy retrieval.
Metadata Analysis: Examination and analysis of the metadata associated with digital evidence, including timestamps, geolocation data, and user information. Metadata analysis provides valuable insights and context that can strengthen the evidentiary value and support investigative conclusions.
Collaboration and Workflow Management: Platforms and tools that enable collaboration among investigative teams, allowing secure sharing, annotation, and discussion of digital evidence. Workflow management features ensure a structured and efficient progression of the investigative process.
Analysis and Visualization: Advanced analytics capabilities to process and analyze digital evidence, uncover patterns, and generate visualizations that aid in understanding complex relationships and connections.
Reporting and Presentation: Tools and templates for generating comprehensive reports and presentations that present digital evidence in a clear, organized, and compelling manner for investigative purposes or in legal proceedings.
Security and Access Control: Robust security measures to protect digital evidence from unauthorized access, tampering, or data breaches. Access control mechanisms ensure that only authorized personnel can view, modify, or delete digital evidence.
Ensuring the Integrity and Authenticity of Digital Evidence
Preserving the integrity and authenticity of digital evidence is of utmost importance in investigations. Various techniques and practices are employed to achieve this objective. Hashing algorithms, such as MD5 or SHA-256, generate unique digital signatures for each piece of evidence, ensuring its integrity remains intact.
Chain of custody procedures establish a documented trail that tracks the handling and custody of digital evidence, preventing tampering or unauthorized access. Digital certificates and digital signatures provide authentication, verifying the source and integrity of digital evidence.
Encryption techniques protect sensitive data during storage and transmission, safeguarding against unauthorized modifications. These measures collectively ensure the trustworthiness and reliability of digital evidence throughout the investigative process.
Overcoming Challenges in DEM Implementation
Implementing Digital Evidence Management (DEM) systems can be complex, but overcoming challenges is essential for successful implementation. This includes addressing technological complexities by ensuring interoperability and providing comprehensive training to personnel.
Managing the volume and variety of data requires robust storage and processing capabilities. Data privacy and security measures, such as encryption and access controls, must be implemented to safeguard digital evidence. Promoting training and adoption among investigators and personnel is crucial for maximizing the benefits of DEM. By addressing these challenges head-on, organizations can effectively implement DEM systems and streamline their digital evidence management processes.
Conclusion: Embracing the Power of DEM in Investigations
Digital Evidence Management (DEM) holds immense potential to transform the way investigations are conducted. By overcoming challenges and implementing robust DEM systems, organizations can unlock numerous benefits. DEM streamlines the management of digital evidence, enhances collaboration among investigators, ensures the integrity and authenticity of evidence, and improves the overall efficiency and effectiveness of investigations.
As the volume and complexity of digital evidence continue to grow, embracing DEM becomes crucial for investigators to navigate this evolving landscape successfully. By leveraging the power of DEM, organizations can harness the full potential of digital evidence, uncover valuable insights, and facilitate fair and accurate outcomes in investigations.
As technology advances, it is imperative that law enforcement agencies, legal professionals, and organizations recognize the significance of DEM and invest in its implementation. By doing so, they can embrace the power of DEM to enhance the investigative process, promote justice, and stay at the forefront of digital investigations in the modern era.
Try our Debt Resolution solutions today Request a Demo